In a world where technology seamlessly integrates into the fabric of our daily lives, wearable technology stands at the forefront of this digital evolution. Imagine a future where your smartwatch not only tracks your heart rate but also provides secure communication with your smartphone and beyond. The narrative of wearable technology’s secure pairing is shaping up to be both an intriguing and crucial aspect of this journey. As we delve into this topic, let’s uncover the intricacies and impacts this development brings to our tech-driven society.
The Importance of Secure Pairing in Wearables
Once, in a bustling city, Emily relied on her smartwatch to track her health metrics and guide her through her daily routine. She appreciated how smart and powerful these tiny, wrist-worn devices were. Yet, in the back of her mind lingered the story of a friend who experienced a data breach. This propelled her into the realm of secure pairing of wearable technology.
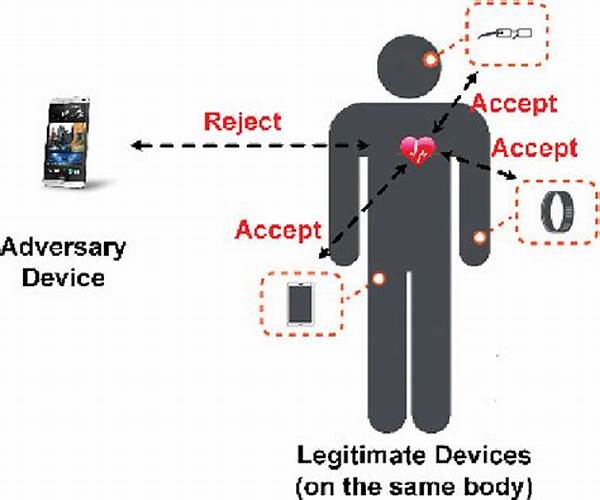
Secure pairing of wearable technology isn’t just a technical concept; it’s the backbone of our trust in these devices. Imagine wearing a device that faithfully logs personal data, from your location to health statistics, all while ensuring this information is accessible only to you and selected, authorized systems. The pairing process must involve comprehensive encryption protocols, providing a fortress against potential threats. Companies and developers are driven by stories like Emily’s to innovate secure practices, building architectures that not only protect data but also empower users with peace of mind during every interaction with their wearables.
As Emily continued her journey, she discovered that the secure pairing of wearable technology went beyond mere privacy protection. It was about harmony between devices, seamless and uninterrupted communication providing a productive experience unblemished by security worries. Each step in her journey echoed the importance of this secure pairing process, ensuring she was connected in a world that values her security as much as her fitness goals.
Achieving Secure Connections with Wearables
1. In the bustling tech industry, ensuring the secure pairing of wearable technology becomes paramount as potential vulnerabilities could compromise personal data, prompting industry insiders to prioritize robust encryption.
2. The secure pairing of wearable technology is often compared to a silent guardian shielding sensitive interactions, drawing parallels to fortresses that protect with unyielding strength and foresight.
3. Tales of users whose data was leaked underscore the exigency for secure pairing of wearable technology, transforming it from a feature to an indispensable security measure.
4. The seamless and secure pairing of wearable technology creates a dance of digital symbiosis, where every interaction strikes a balance between innovation and safety.
5. Secure pairing of wearable technology forestalls countless silent threats, ensuring users can navigate the benefits of connectivity without compromising their well-being or personal data.
Challenges in Securing Wearable Tech Pairings
For Juliana, a tech-savvy athlete who depended on her fitness tracker, trust in the secure pairing of wearable technology was non-negotiable. Her world revolved around the data-driven insights these wearables provided, but she often pondered the real security provided by these everyday companions. Her concerns were not unwarranted.
As she researched more, she found that the road to achieving secure pairing of wearable technology often met with hurdles such as outdated software, weaknesses in encryption standards, and the constant evolution of cyber threats. Wearable devices, by their very nature, required constant connectivity, increasing the risk landscape for potential breaches. Developers faced the challenge of creating secure pairings that were not just immediately effective but were able to evolve against future threats poised by ever-adapting cyber criminals.
Juliana’s journey wasn’t just one of discovery; it was a call to action in the tech industry. It highlighted the necessity of fostering cooperation between consumers and developers. Her narrative emphasized the profound relationship between a user and their device where trust is continuously nurtured through ongoing updates and vigilance in secure pairing practices.
Stories of Ensuring Secure Pairing
1. Within the confines of a small innovation lab, Anne concocted pioneering algorithms to bolster the secure pairing of wearable technology, drawing inspiration from classic tales of protectors.
2. When a major data leak hit the industry, it became a cautionary tale leading tech companies to overhaul how secure pairing is integrated into wearable technology.
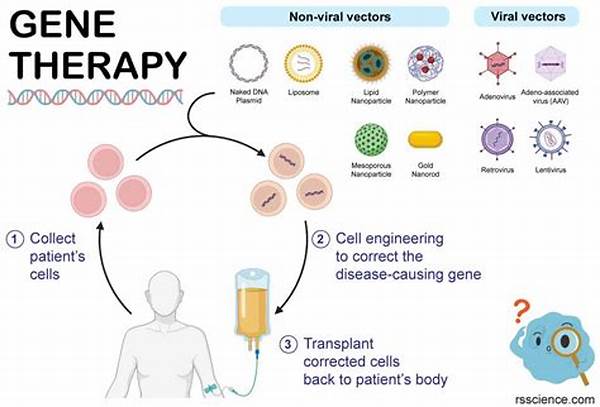
3. A university study unearthed intriguing ways to maintain the secure pairing of wearable technology using biometrics, presenting a future where every device becomes intrinsically personal.
4. Secure pairing of wearable technology parallels historical encryptions, reminding users of the age-old battle between codemakers and codebreakers.
5. Oliver’s quiet innovation in secure pairing of wearable technology was fueled by the memory of a security breach that almost cost him dearly.
6. In an interconnected cityscape, vigilant secure pairing of wearable technology ensures personal data flows safely through the digital hustle and bustle.
7. Behind every securely paired wearable lies a tale of relentless testing and refinement, sometimes likened to crafting an impenetrable shield.
8. As users explored new devices, each brought stories of varying experiences with secure pairing of wearable technology, forming a symphony of trust building.
9. With dazzling technological advancements came the unseen but vital narrative of secure pairing of wearable technology, echoed through experiences of users and creators alike.
10. The manifestation of secure pairing of wearable technology is akin to an evolving narrative, one that intricately weaves security and user experience in a continuous loop.
Enhancing User Trust Through Secure Pairing
In the ethereal veil of innovation, the secure pairing of wearable technology represents an unwritten promise between developers and users, a covenant of safety and trust. This was a narrative John, a tech enthusiast, found himself drawn to as he juggled his work and personal life with the help of assorted gadgets neatly paired to serve his dynamic needs. Like a symphony that required both harmony and precision, the secure pairing ensured all his devices sang in perfect coordination, safeguarding his personal symphony of data.
John’s trust was paramount, built upon years of investing in wearables that functioned in tandem with life’s high and low notes. Yet, every pairing had a tale—a unique process that involved not just direct correspondence between devices but multifaceted tests to ward off any lurking threats. The intuitive dance of machine learning and AI played a subtle yet profound role, anticipating and preempting potential security hiccups.
Secure pairing of wearable technology demanded an unyielding commitment from tech architects to fulfill their end of the pact. It served as a lighthouse for users teetering on the edge of adopting new technologies, paving a confident path that ensured the promise of safety wasn’t mere rhetoric but an irrefutable bond of assurance restored with each securely paired connection users encountered.
Secure Pairing: Weaving the Web of Connectivity
One might liken the secure pairing of wearable technology to a transparent canvas, on which a vivid mosaic of connectivity narratives are painted. Inherently complex, each device tells its own tale of how secure pairing unravels—from initial handshakes fortified by rigorous authentication to robust encryptions that transform data exchanges into encrypted whispers.
As Paul analyzed the transformation of technology in context, the secure pairing of wearable technology emerged as one of the silent architects of the Internet of Things ecosystem. It was crucial, he noted, for consumers to understand that the luxe of effortlessly paired devices was underpinned by layers of security protocols and consistently audited pairing processes. Every secure pair symbolized a commitment, a vibrant web meticulously woven by developers to ensure inter-device communications can withstand subtle manipulations and overt attacks alike.
Caught in the narrative of his own journey with wearables, Paul found himself contributing to a larger story while appreciating the technological advances that supported personal privacy amid the kaleidoscope of interconnected tech. Secure pairing wasn’t just code—it was kinship between innovation and trust, a foundational bedrock ensuring every interaction was framed by a reassuring veil of security.
By embracing tales of innovation, strength, and the symbiotic nature of technology and security, secure pairing of wearable technology continues to carve its narrative into the ever-evolving digital landscape.